How to store encryption key in database images are ready in this website. How to store encryption key in database are a topic that is being searched for and liked by netizens today. You can Download the How to store encryption key in database files here. Download all royalty-free vectors.
If you’re searching for how to store encryption key in database images information connected with to the how to store encryption key in database keyword, you have pay a visit to the ideal site. Our site always gives you hints for seeking the highest quality video and picture content, please kindly surf and locate more informative video articles and graphics that match your interests.
How To Store Encryption Key In Database. 05112019 A better scenario would be to collect names mails and phone numbers encrypt and store them in a database hosted on a server different than the web server. Currently you can store a CMK in the Windows certificate store Azure Key Vault or a hardware security module HSM. The encryption of this data consists of using an algorithm to convert text or code for it to be unreadable. 19072021 The default configuration Oracle-Managed Keys stores the master encryption keys in a wallet file locally on the database servers.

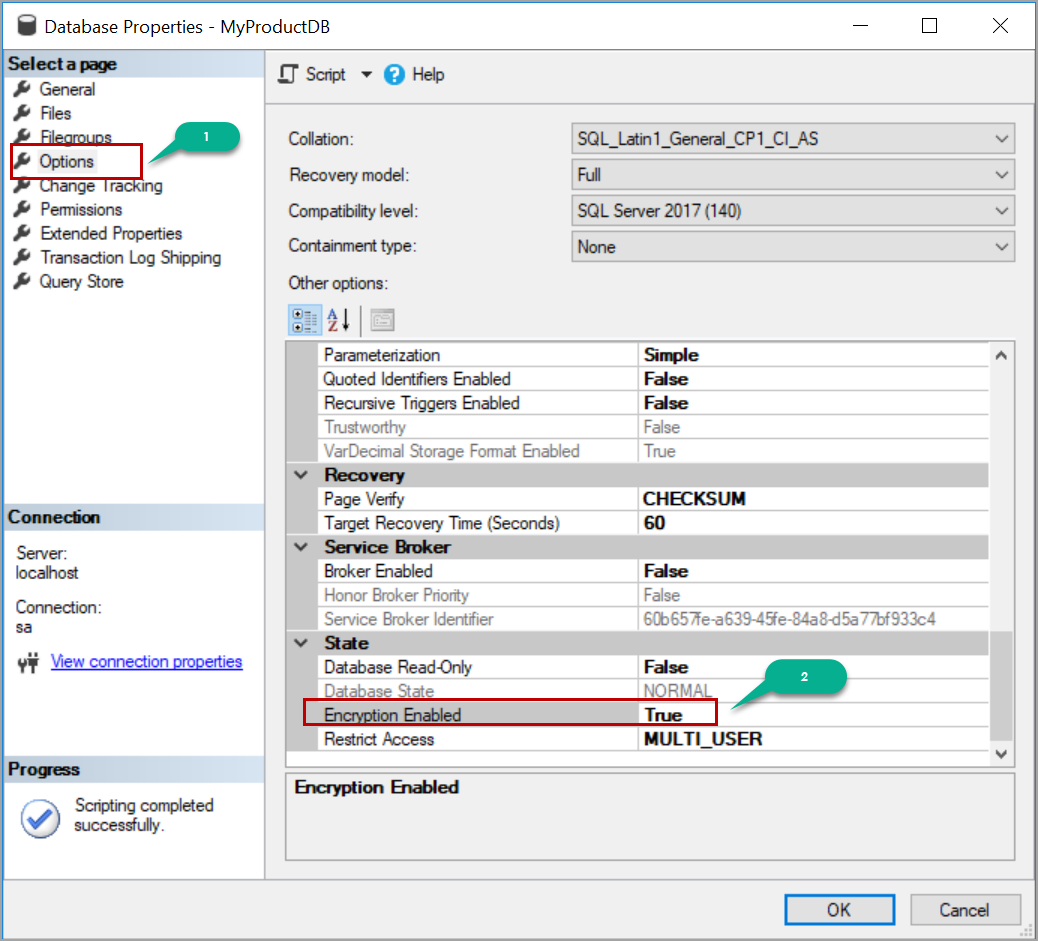 Restoring Transparent Data Encryption Tde Enabled Databases On A Different Server From sqlshack.com
Restoring Transparent Data Encryption Tde Enabled Databases On A Different Server From sqlshack.com
How to store encryption keys for example in the files. 10112008 If you need the registry key as well you can always use the following connection string. Generally hashing requires a salt for each record. This tutorial shows how to store your keys in the Windows certificate store. Function encrypt key sourceData const iv Bufferalloc16 0. 06092021 Data in an AIS database can be stored in encrypted form to deter it unethical or fraudulent use.
Let encrypted cipherupdatesourceData binary binary.
Type in the encryption key when you start up store it in memory. 14032017 To enable the automatic decryption of the database master key a copy of the key is encrypted by using the SMK. The encryption of this data consists of using an algorithm to convert text or code for it to be unreadable. Initialization vector const cipher cryptocreateCipherivaes-192-cbc keycipherKey iv. 07052019 Now we can use the generated key to encrypt any data. 20082014 Otherwise it would be easy to find all the common data in a database and deduce a pattern from the encryption.

 Source: docs.oracle.com
Source: docs.oracle.com
06092021 Data in an AIS database can be stored in encrypted form to deter it unethical or fraudulent use. 23022018 If what you provide the user is a combination of primary key and API key you can then securely store the API key. Similar to the option above but also different. Currently you can store a CMK in the Windows certificate store Azure Key Vault or a hardware security module HSM. Note that it is required to use a Password Based Key Derivation Function PBKDF such as PBKDF2 bcrypt or scrypt to create a secure password hash given the normal security level of a password.
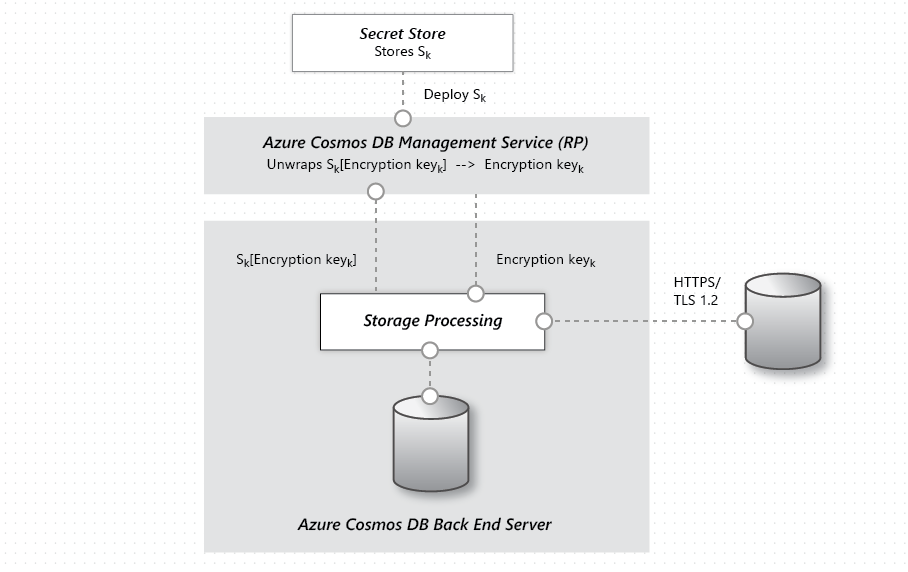 Source: docs.microsoft.com
Source: docs.microsoft.com
Type in the encryption key when you start up store it in memory. Generally hashing requires a salt for each record. Then use that as key for encrypting the private key. 05112019 A better scenario would be to collect names mails and phone numbers encrypt and store them in a database hosted on a server different than the web server. Function encrypt key sourceData const iv Bufferalloc16 0.
 Source: docs.oracle.com
Source: docs.oracle.com
The copy of the DMK stored in the master system database is silently updated whenever the DMK is changed. 06092021 Data in an AIS database can be stored in encrypted form to deter it unethical or fraudulent use. Putting the encryption key anywhere in the database or accessible to the database frequently defeats the purpose of encryption because anyone with access to the database can simply decrypt the data. 20082014 Otherwise it would be easy to find all the common data in a database and deduce a pattern from the encryption. Function encrypt key sourceData const iv Bufferalloc16 0.
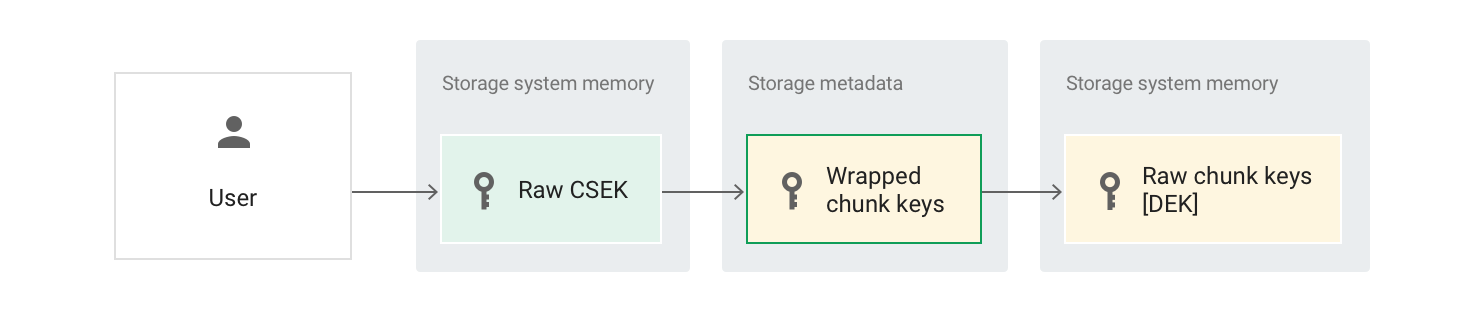 Source: cloud.google.com
Source: cloud.google.com
Putting the encryption key anywhere in the database or accessible to the database frequently defeats the purpose of encryption because anyone with access to the database can simply decrypt the data. 20082014 Otherwise it would be easy to find all the common data in a database and deduce a pattern from the encryption. How to store encryption keys for example in the files. Remember to use the algorithm correctly. The encryption of this data consists of using an algorithm to convert text or code for it to be unreadable.

There are different hashing algorithms. Now Oracle also supports the integration with the OCI Vault Service where you are able to create and control your TDE master encryption keys or import your existing ones. The encryption of this data consists of using an algorithm to convert text or code for it to be unreadable. Ie it is clear that you can throw on the disc but in the event of a compromise of access together with the base leaked key. 19072021 The default configuration Oracle-Managed Keys stores the master encryption keys in a wallet file locally on the database servers.
 Source: thesslstore.com
Source: thesslstore.com
Note that it is required to use a Password Based Key Derivation Function PBKDF such as PBKDF2 bcrypt or scrypt to create a secure password hash given the normal security level of a password. 17032021 Data at-Rest Encryption Data stored in a system is known as data at-rest. Simply store an additional salt and perform the password hash. 23042020 The Master Key Configuration page is where you set up your CMK and select the key store provider where the CMK will be stored. Currently you can store a CMK in the Windows certificate store Azure Key Vault or a hardware security module HSM.
 Source: documentation.commvault.com
Source: documentation.commvault.com
Ie it is clear that you can throw on the disc but in the event of a compromise of access together with the base leaked key. Simply store an additional salt and perform the password hash. Function encrypt key sourceData const iv Bufferalloc16 0. It is stored in both the database where it is used and in the master system database. Remember to use the algorithm correctly.
 Source: docs.oracle.com
Source: docs.oracle.com
The encryption keys should be stored at. 19072021 The default configuration Oracle-Managed Keys stores the master encryption keys in a wallet file locally on the database servers. Type in the encryption key when you start up store it in memory. 10112008 If you need the registry key as well you can always use the following connection string. Simply store an additional salt and perform the password hash.
 Source: kohera.be
Source: kohera.be
The encryption of this data consists of using an algorithm to convert text or code for it to be unreadable. Then use that as key for encrypting the private key. To safely store your data in a database youd start by generating a strong secret key. Remember to use the algorithm correctly. I think that is probably more correct before running database to connect to some remote network resource folder which is the key start the database and after startup to unmount this share.
 Source: sqlshack.com
Source: sqlshack.com
If Oracle permissions are enough to prevent the user from decrypting the data they would be enough to prevent the user from selecting the unencrypted data. Government regulations including HIPPA require some forms of private or sensitive data to be transmitted in encrypted form. The encryption of this data consists of using an algorithm to convert text or code for it to be unreadable. It is stored in both the database where it is used and in the master system database. If Oracle permissions are enough to prevent the user from decrypting the data they would be enough to prevent the user from selecting the unencrypted data.
 Source: docs.microsoft.com
Source: docs.microsoft.com
07052019 Now we can use the generated key to encrypt any data. There are different hashing algorithms. Remember to use the algorithm correctly. Since the key is effectively a password hashing should be sufficient and is recommended. The encryption keys should be stored at.

This site is an open community for users to do sharing their favorite wallpapers on the internet, all images or pictures in this website are for personal wallpaper use only, it is stricly prohibited to use this wallpaper for commercial purposes, if you are the author and find this image is shared without your permission, please kindly raise a DMCA report to Us.
If you find this site beneficial, please support us by sharing this posts to your preference social media accounts like Facebook, Instagram and so on or you can also save this blog page with the title how to store encryption key in database by using Ctrl + D for devices a laptop with a Windows operating system or Command + D for laptops with an Apple operating system. If you use a smartphone, you can also use the drawer menu of the browser you are using. Whether it’s a Windows, Mac, iOS or Android operating system, you will still be able to bookmark this website.